Inspired by Kerberos Golden Tickets, I researched what would be necessary to maintain long-term access into a Kubernetes cluster–effectively how to craft Kubernetes Golden Tickets. This research yielded the Kubernetes Spoofilizer: a tool which can create arbitrary ServiceAccount tokens, as well as administrative user certificates!
Setup is straightforward: on a compromised Kubernetes cluster, copy the Certificate Authority certificate & key, along with the ServiceAccount key from one of the control plane nodes, and now you can create tokens and user certificates with any level of access. And with any expiration times you want!
[ Read more... ]
The DHEat denial-of-service vulnerability involves sending a large number of Diffie-Hellman (DH) public keys to a peer, causing it to perform many unnecessary modular exponentiations and wasting CPU resources (in fact, the attacker can simply send random numbers instead of real DH keys to avoid incurring the computational penalty themselves). Because the DH handshake occurs before authentication in many network protocols (such as SSH), the attack can be conducted anonymously. And interestingly, as the size of the DH modulus increases, the brute-force security of the key exchange also increases, but so does the susceptibility to the DHEat attack since larger (and more expensive) modular exponentiation is required.
[ Read more... ]
Recently I released ssh-audit v2.3.0 with new policy configuration checking support. This makes IT admins’ lives easier, since it boils down the output of ssh-audit to a simple pass/fail answer.
Standard Scans vs Policy Scans
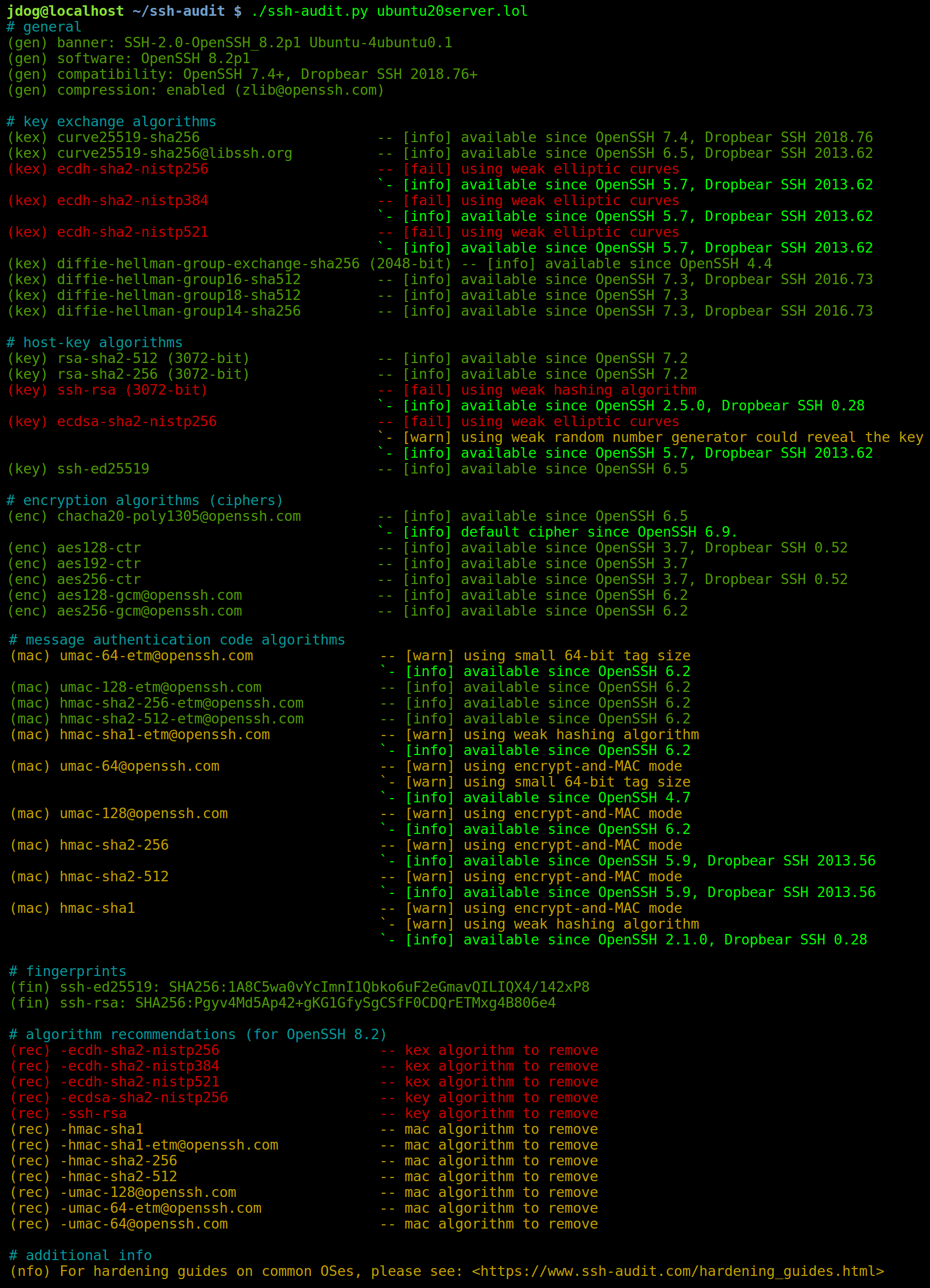
Normally, ssh-audit goes through the list of cryptographic algorithms supported by the server, and rates each one. Here’s example output against an unhardened Ubuntu Server 20.04 system:
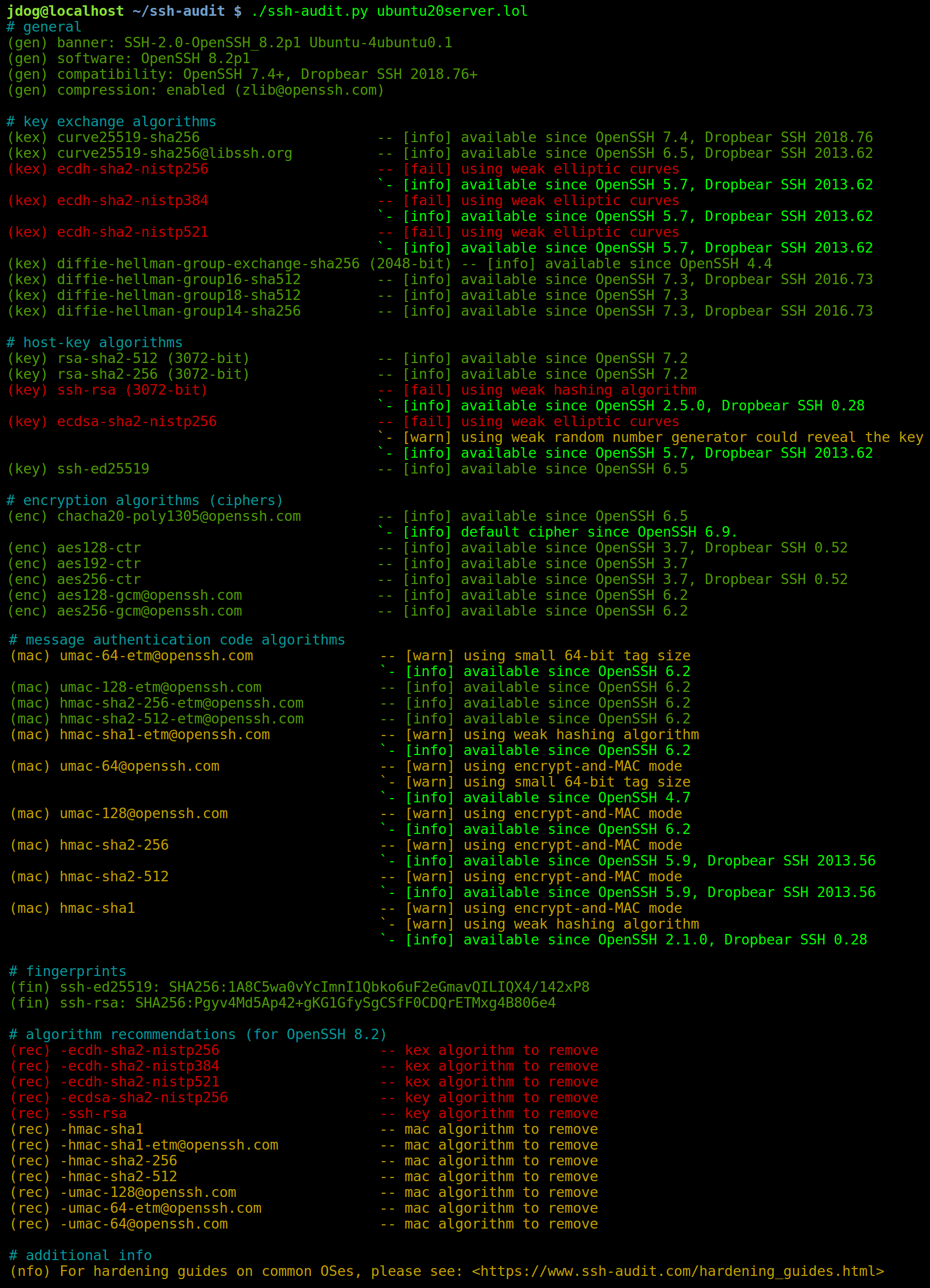
After applying the right hardening guide for this OS, ssh-audit’s output looks like this:
[ Read more... ]
I reported a serious local privilege escalation flaw in GOG Galaxy Client on April 28, 2020, but my follow-up investigation (detailed below) found the vendor’s fix to be insufficient. By updating the proof-of-concept exploit code, it is possible to execute arbitrary commands as SYSTEM in GOG Galaxy Client v2.0.13 through v2.0.15 v2.0.19 (the latest as of this writing).
GOG did not reply that this issue was officially fixed, although changes were silently made at some point after the v2.0.15 release to stop the provided proof-of-concept tools from working. It is suspected that only minor changes were made to frustrate exploitation; an investigation is ongoing (See update below).
[ Read more... ]
The GOG Galaxy client is video game management software published by GOG. An audit of its security (for versions 1.2.64 and 2.0.12.48) revealed a critical local privilege escalation flaw that allows the execution of arbitrary commands as SYSTEM.
GOG fixed this issue in v2.0.13, released on February 25, 2020. Unfortunately, I was not notified of this until April 28, 2020–the 90-day deadline as per Google’s vulnerability disclosure policy. It is unknown if a fix was issued for the v1.2 branch.
[ Read more... ]
Today, on behalf of the Rainbow Crackalack Project, I’m proud to announce the immediate availability of NTLM 9-character rainbow tables!
A Brief Recap
Ten months ago, in June 2019, I released the Rainbow Crackalack v1.0 software along with NTLM 8-character tables for free via Bittorrent. The tables could (and still can) be obtained by purchasing them on an SSD hard drive as well.
At the same time, I announced a Kickstarter project to raise at least $3,000 to purchase equipment to generate 9-character tables with. While the project failed to reach its funding goal, people from around the world nevertheless volunteered to generate tables for the project. I’ve been generating, collecting, and processing them in the last ten months, and now we’ve reached the original goal: tables that crack NTLM 9-character passwords at an efficiency of 50%!
[ Read more... ]
It’s been known for years now that SSH servers can (and should) be hardened by removing weak default algorithms. For example, recent versions of OpenSSH ship with algorithms suspected of being back-doored by the NSA (i.e.: ECDSA with the NIST P-curves), along with other algorithms with sub-128bit security levels.
But did you know that client software can be hardened too?
Why Harden Client Software?
In a world where all servers are properly hardened, there would be no need to re-configure client software. However, server hardening is unfortunately more rare than it should be, and you can only do it for machines you directly control. In that case, it’s very useful to upgrade your client’s defaults so you have assurance that only strong connections will be made.
[ Read more... ]
Today marks the release of ssh-audit v2.0.0! This tool audits SSH server configurations and highlights vulnerabilities in the following areas:
- Host key types & sizes
- Key exchange algorithms
- Ciphers
- Message authentication codes (MACs)
It is especially useful since the defaults on many systems are, let’s say… less than ideal.
Here’s example output against an older CentOS 6 machine:

Aside from cloning the GitHub repository, you can obtain ssh-audit from PyPI as well:
[ Read more... ]
Today marks the release of Rainbow Crackalack v1.0!
This project was started to fill a gap in the password-cracking toolset. Rainbow tables were popular up until around 2012, when they began to be phased out in favor of rules-based cracking. While newer techniques are indeed very effective, rainbow tables still excel at cracking fully random passwords. Humans don’t typically use fully random passwords, but for high-privilege accounts (such as Windows domain administrator accounts), they are more common. If rules-based password cracking techniques fail, then a viable fall-back is a rainbow table attack. Hence, both methods are complementary to each other.
[ Read more... ]
A lot of administrators install the SSH service and assume its in top shape. What they don’t realize is that system packages tend to be optimized for compatibility, not security. While a lot of systems include defaults that are fine for most cases, there is still a lot of room for improvement–especially for high-security environments.
Depending on how old the package for your distribution is, the default configuration may have the following problems:
[ Read more... ]
A few months ago on an internal pentest, I wanted to do an MITM attack on SSH tunnels to capture credentials. Besides the out-dated SSHv1 downgrade trick, the only thing I could find was the JMITM2 tool. But not only was it last updated in 2004, I couldn’t get it to work either.
So I sat down and wrote a patch for OpenSSH v7.5p1 (the latest version) to make it do what I want. Now with a little ARP spoofing, you can capture their plaintext password and log a victim’s entire session! Of course, their SSH client will complain that the server key has changed, but guess what many/most people do in that situation? The overwhelming majority of the time, that warning is caused by an OS re-install or re-configuration, so people tend to ignore it. Big mistake.
[ Read more... ]